#best object storage software
Explore tagged Tumblr posts
Text

Spictera, a premier cybersecurity company, delivers top-notch protection against cyber threats. Specializing in advanced threat detection and response, Spictera provides tailored solutions to safeguard your digital assets. Trust Spictera for comprehensive cybersecurity services that ensure the integrity and security of your business operations.
0 notes
Text
Malware I
Reveria rolled her eyes, servos clicking in a way only she could hear, blinking apathetically as she turned her music up. She understood the stares, as much as she despised them. Mugorra didn't get many synthetics like her, especially on Outer Ring trains. The long, heavy shawl she wore covered most of her slender body, both to keep the sand out of her joints and to deflect any further stares.
She wasn't exactly subtle – people of all kinds drifted through here, but being a foot taller than the average human with glowing orange eyes and an extra set of arms made one stick out.
The job was simple. Get in to the storage container, get the silver case, and get out. Perhaps a tier below the usual bloodshed for a KALI-6 class synthetic, but she was doing her best to lay low and take whatever jobs would get her least noticed.
She was trying to sit somewhat still. The case wasn't large, but it was stuffed under her shawl at the moment, and occasionally a corner poked out. She shifted her grip again, moving her hand on the handle for a more comfortable position.
ding
She heard the quiet internal chime and froze. That noise meant something had connected to her. Nothing should have been able to. The shawl had a Faraday cage sewn into the fabric, and it was snapped snug around her. Wireless signals shouldn't have been able to get through, unless-
Shit. The fucking case. She ducked down into the shawl quickly to inspect the case. When she had taken it, she hadn't looked thoroughly enough at it, and had apparently missed the quick contact port in the handle that now stared back at her, her thumb an inch from it after swiping across it when she shuffled it in her secondary arms.
[Download Requested]
Fuck. Every urge in her body was screaming at her to hurl the case away. She had to maintain a facade of order. If she got the case out of the shawl it would block the download, but she couldn't take it out without raising suspicion. This was a poor district. No one carried anything like it here. She couldn't even cancel or acknowledge the download request because she was set up for somakinetic controls and that kind of movement was out of the question.
[Download Proceeding]
What the fuck was she supposed to do about that? She couldn't contact her handler this far underground, and she doubted he'd even know how to fix a software issue with her. She'd foregone her normal backers and picked up a quick contract in the area from a sketchy Vinteran because she was trying to stay within city limits. Something had seemed wrong with him the entire briefing.
Many species got edgy around synthetics, especially KALI models, but this was something else. The whole time they talked, his eyes kept flicking to the door and across the room. Anywhere but her. She wasn't that intimidating, and most people in this business had dealt with scarier synths than her. She'd seen his arms. For as many tattoos as he had, each signifying a kill, she knew he'd seen worse.
Wait. There was another tattoo. Three triangles surrounding an S. Fuck. She sighed, more out of annoyance than actual worry. That slimy, two-faced scaly piece of shit was a Trigonalist. Of course. She'd worked with them before, but it was always born of desperate necessity. "Terrorist" was a strong term, but they weren't the best people out there.
That explained the job, then. She'd wondered why this case was being treated as so important. Lab-grown neurons were a dime a dozen, even out here, and a case that could hold maybe five or six brainslabs maximum couldn't have been worth what she was getting paid to retrieve it, especially since they were blank. But if they could get a small object inside her shawl and download something onto her, like remote access software or a location log?
Well, a KALI-6 class synthetic was decidedly not a dime a dozen anywhere.
[Download Complete]
She instinctively braced up, preparing herself. She'd been cyberattacked before, and she'd lived. She knew what to expect. It was probably going to either be excessive, disabling pop-ups or a logger she could sift through herself and cull later. Nothing too hard to handle.
She wasn't expecting the sharp, drowning techno in her ears to fade out and replace itself with soft jazz. Nor was she expecting the silk-smooth voice that seemed to rebound around the narrow train car, reverberating from everywhere and nowhere.
Hi, sweetie~
She tried to move her eyes, looking around for the speaker without moving her head.
Don't bother with that, darling, I'm still miles away from you! I'm surprised I could even get a connection down in those tunnels!
No one else seemed to be reacting to it. Everyone's faces were still cast down, trying not to make eye contact. It was too late at night for social interaction, especially with this trigger-happy crowd. Accidents happened down here all the time.
Oh, no one can hear me except you! Don't bother asking them for help. It'd be a shame if anyone were to think the big scary killsynth was attacking them. It would probably get... messy.
No one could hear the voice except for Reveria. That made it easier. If it was coming straight from an external source and being processed as speech, that was likely a remote access software. If she could activate a virus scrubber and get into a dead zone, it'd be easy enough to disable.
Oh no you don't, cutie. I'm all clientside. Besides, we're having fun, right?
She needed to know who this was. If she could hold onto this, she could take it into an Enforcement station. Granted, they likely wouldn't be happy to see her, but they'd most likely let her off for bringing in a Trigonalist. Disabling her external speakers, she cast her voice across the link.
Are you a synth? It was hard to know these days. Speech synthesizers had gotten so advanced since Reveria's assembly days.
No, I'm fully human, especially the bits that matter~
What's that supposed to mean?
Watch this! A new screen flicked open, overlaying above the occupants of the train car, showing a video at half transparency. It was enough to pick out details, at least. It just seemed to be... shapes? What was she looking at?
Oh. Oh, six suns. That was human genitalia. Close to the camera and at a strange angle, but still recognizable. Reveria watched with a combination of incredulous amazement and horror as the dripping hole a foot from her face was split open by pale, slender fingers capped with electric blue nails, index and pinky resting gently on the thighs as middle and ring curved delicately through the glistening pink flesh.
Could a synth do this? Technically yes, since most synths were modular enough to install... equipment down there, and some even accessorized with it as a fashion statement, changing it out by the day, but that was beside the point.
Is... is this live? In real time, I mean?
Obviously! Only the best for a pretty girl like you! The other hand, previously out of the camera, descended into the shot holding something that made Reveria's temperature jump up a bit.
Synths didn't really have genitalia, but plenty of aftermarket manufacturers made compatible items for them. She was ashamed to admit she owned a few of different makes and models, but a girl had needs. The voice in her head was holding one of Placebo's Bruiser models, one of Reveria's favorites. It was long and slender, with a ridged underside that featured a camouflaged electroconductive strip that boosted the signal from the partially conductive outer shell.
Said signal strength was entirely customizable for the enjoyment of the wearer, meaning when the voice ran her fingers slowly up the length then circled them around the pointed end, Reveria felt it all as she tried desperately to not buck her hips into the sensation, her body involuntarily seeking more stimulation for the appendage she didn't even have connected. Fuckin' wireless transmission...
Aww, does that feel good? Don't worry, I'll help you feel it~ Reveria tried to brace herself as the feminine words in her ear ran their fingers along the length again before angling it and pushing just the tip into herself. To the synth's immense embarrassment, she couldn't physically stop her hips from slamming forwards, immediately thanking whatever spectral forces existed that no one on the train noticed.
Oh? Someone wants me, huh? Here you go, then!
The synth stifled a scream as the voice slammed the entire length in at once, arching her back slightly for a better angle as the synth was forced to watch and feel all of it. The voice, for her part, was clearly also feeling it, as the constant noise attested. Reveria couldn't think clearly. No matter where she turned her head, she could see the human practically bouncing on it, to speak nothing of the feeling which only grew stronger as the human leaned forward. The synth could feel the human touching her, one hand on her shoulder and the other pressing her into the seat with a force that she knew wasn't real but certainly felt tangible enough.
She got a momentary relief from the constant whimpering in her ear when the brakes of the train activated, the loud screech drowning out all but the words, This is your stop! Don't miss it!
The moment the train had stopped, the needy whines returned. Reveria managed to stumble to her feet, shaking like a drunken Turvoss, and stagger off the train. She had barely made it to the platform before the fire in her midsection caught up to her and her legs practically buckled as the world was drowned out in a sea of white.
Fuck, Revi, don't just stop! I need you please don't stop now! The sensation of the length being ensheathed again was so much more powerful now, and if Reveria had been halfway lucid at this point she would have picked up on the fact that the human knew her name. As it was, that was far more thinking than she was capable of. All she could think about was getting home. She managed to pool her brain function enough to find and activate the tracker beacon in her rented room, the slender white line tracing out a path in front of her that she attempted to follow, one step at a time.
The feeling was overwhelming her. It was unprofessional, but she needed some time alone. If she had anything attached to relieve herself with, she likely would have lost her composure and done it right there in the station. As it was, she just moved through the station as fast as she could, shaky, desperate movements drawing stares that she was too deep in a world of need to notice or care about.
She was halfway up the stairs to exit the station when it happened again, her entire body twitching hard then going limp as she frantically grabbed a rail to avoid falling. The voice just laughed in her ear as she did. It was only three blocks to her building. She could make it.
She wasn't even up the stairs when the next one hit. They were getting faster and faster, her increased sensitivity after each making it easier to drive her over the edge for the next.
You gotta get home, okay? I need you to pick something out and fuck me for real~
Three blocks. It was three blocks.
This was the door. The white strip on the street took a sharp left through the narrow arch. She crossed the threshold, holding the doorframe for support as she climaxed again. How many times had she? Thinking about it was too hard. There was nothing in her head anymore except for that delicious whimpering that seemed to increase in intensity along with her. She just had to take the elevator up to the eighth floor and get into her room, then she could cut the signal.
The hallway looked the same as it always did. Bare. Stumbling to her door, she tried the knob. Locked. She just snapped it off. Any measure or restriction of her own strength was gone. The door swung open.
Something was wrong. Her brain was getting sluggish, but she retained enough evidence to realize this wasn't her room. The sand-brown walls she should have seen were dark and lit with purple LEDs, and the furniture was all arranged wrong. Soft jazz was playing.
She had a sudden break of clarity, and felt cold all of a sudden as the figure sitting in the back of the room, lit from behind by a computer monitor, pulled the toy from within herself and tossed it over. Reveria's hand instinctively shot up and caught it, the liquid on it glinting in the harsh hallway light. She checked the tracker beacon she had been following. Where she had expected reveria.home in the namespace, she saw instead DEN1ZEN. This wasn't her building.
Hi, Revi~
#monster fucker#terato#hypnosis#(kinda)#synthetic#robot#robotification#robotization#wlw nsft#exhibition#fantasy nsft#sci fi nsft
239 notes
·
View notes
Text
Why Scribbook is the best writing tool I know

At least it's the best for me. Your mileage may vary, etc. etc.
Scribbook is an online writing studio (it doesn't have an app as far as I'm aware), developed in French by one guy, and can be accessed here.
it's FREE
You heard me. The first 5 MO are, at least. After that there's a paid option that unlocks a few other features along with more storage space, but it took me 4 years to even reach that milestone. So you're good.
2. It has all the things you need to write
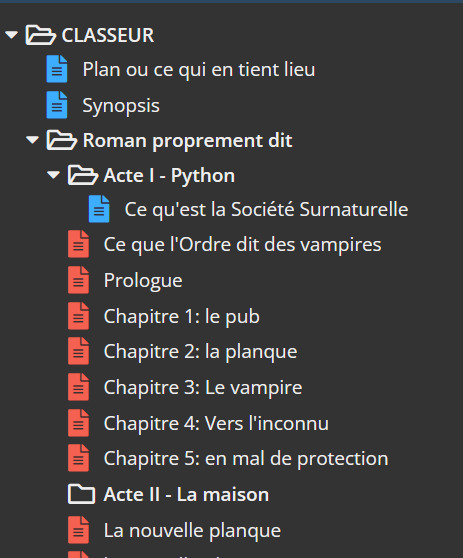

Some people are organized. And then there's me.
At the very beginning, you can chose a template for your novel (or just start from scratch). From there, you can create files, scenes, etc. and just move them around (a map view is available, which might be useful to some others than me). Also the option to write the synopsis on a text file. Personally I use that to write notes to myself for future editing.
The rest is basic, important stuff: text formatting, page breaks, etc. There's a sepia and a dark mode as well.
3. You can write anywhere
Unlike Scrivener, you can access it from any computer or phone, and unlike Google docs, it won't suggest stupid edits and/or spy on you. Very useful when you're on the go and writing at work writing in the break room.
4. It doesn't have TOYS
Toys are what I call things that are not mandatory for your writing project but are so fun to use and so good at make you think you're being productive when in fact you're just procrastinating. You know what I'm talking about: family trees, map editor, encyclopedia, etc. Apart from a verse counter (which makes writing alexandrins very easy) and an option for character pages, nothing of the sort here. You're here to WRITE, not to pretend to write. Oh, and there's a fullscreen mode to avoid distraction. A godsend.
5. You can set objectives and see your progress
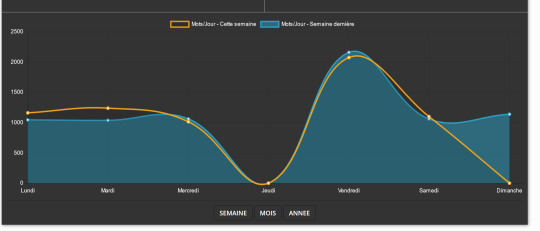
The consistency of a persistent hunter
There's a wordcount and you can chose to set it as you like. 300 words a day, 1000 a week, 8000 a month, whatever. I found it very good to condition myself to write; now I just know that 1 hour of work = roughly 1000 words. You're also rewarded by a nice graphic that tells you how much you've worked this week, month or year.
To summarize, I'd say that while some won't like the fact that you're writing on a website and not on your own computer, the pros outweight the cons. It's a free tool, with the same functionalities as a paid software like Scrivener or Campfire, and it's in French, so yay baguette
4 notes
·
View notes
Text
"DCA"(DIPLOMA IN COMPUTER APPLICATION)
The best career beginning course....

Golden institute is ISO 9001-2015 certified institute. Here you can get all types of computer courses such as DCA, CFA , Python, Digital marketing, and Tally prime . Diploma in Computer Applications (DCA) is a 1 year "Diploma Course" in the field of Computer Applications which provides specialization in various fields such as Fundamentals & Office Productivity tools, Graphic Design & Multimedia, Programming and Functional application Software.

A few of the popular DCA study subjects are listed below
Basic internet concepts Computer Fundamentals Introduction to programming Programming in C RDBMS & Data Management Multimedia Corel draw Tally ERP 9.0 Photoshop
Benefits of Diploma in Computer Application (DCA)
After completion of the DCA course student will able to join any computer jobs with private and government sectors. The certification of this course is fully valid for any government and private deportment worldwide. DCA is the only best option for the student to learn computer skills with affordable fees.
DCA Computer course : Eligibilities are here... Students aspiring to pursue Diploma in Computer Applications (DCA) course must have completed their higher school/ 10 + 2 from a recognized board. Choosing Computers as their main or optional subject after class 10 will give students an additional edge over others. Apart from this no other eligibility criteria is set for aspirants. No minimum cutoff is required.

"TALLY"
A Tally is accounting software. To pursue Tally Course (Certificate and Diploma) you must have certain educational qualifications to thrive and prosper. The eligibility criteria for the tally course is given below along with all significant details on how to approach learning Tally, and how you can successfully complete the course. Generally, the duration of a Tally course is 6 month to 1 year ,but it varies depending on the tally institution you want to join. Likewise, tally course fees are Rs. 10000-20000 on average but it also varies depending on what type of tally course or college you opt for. accounting – Accounting plays a pivotal role in Tally
Key Benefits of the Course:
Effective lessons (topics are explained through a step-by-step process in a very simple language) The course offers videos and e-books (we have two options Video tutorials in Hindi2. e-book course material in English) It offers a planned curriculum (the entire tally online course is designed to meet the requirements of the industry.) After the completion of the course, they offer certificates to the learners.
Tally Course Syllabus – Subjects To Learn Accounting Payroll Taxation Billing Banking Inventory
Tally Course
Eligibility criteria: 10+2 in commerce stream Educational level: Certificate or Diploma Course fee: INR 2200-5000 Skills required: Accounting, Finance, Taxation, Interpersonal Skills Scope after the course: Accountant, Finance Manager, Chartered Accountant, Executive Assistant, Operations Manager Average salary: INR 5,00,000 – 10,00,000

"In this Python course"
Rapidly develop feature-rich applications using Python's built-in statements, functions, and collection types. Structure code with classes, modules, and packages that leverage object-oriented features. Create multiple data accessors to manage various data storage formats. Access additional features with library modules and packages.
Python for Web Development – Flask Flask is a popular Python API that allows experts to build web applications. Python 2.6 and higher variants must install Flask, and you can import Flask on any Python IDE from the Flask package. This section of the course will help you install Flask and learn how to use the Python Flask Framework.
Subjects covered in Python for Web development using Flask:
Introduction to Python Web Framework Flask Installing Flask Working on GET, POST, PUT, METHODS using the Python Flask Framework Working on Templates, render template function
Python course fees and duration
A Python course costs around ₹2200-5000.This course fees can vary depending on multiple factors. For example, a self-paced online course will cost you less than a live interactive online classroom session, and offline training sessions are usually expensive ones. This is mainly because of the trainers’ costs, lab assistance, and other facilities.
Some other factors that affect the cost of a Python course are its duration, course syllabus, number of practical sessions, institute reputation and location, trainers’ expertise, etc. What is the duration of a Python course? The duration of a basic Python course is generally between 3 month to 6 months, and advanced courses can be 1 year . However, some courses extend up to 1 year and more when they combine multiple other courses or include internship programs.
Advantages of Python Python is easy to learn and put into practice. … Functions are defined. … Python allows for quick coding. … Python is versatile. … Python understands compound data types. … Libraries in data science have Python interfaces. … Python is widely supported.

"GRAPHIC DESIGN"
Graphic design, in simple words, is a means that professional individuals use to communicate their ideas and messages. They make this communication possible through the means of visual media.
A graphic designing course helps aspiring individuals to become professional designers and create visual content for top institutions around the world. These courses are specialized to accommodate the needs and requirements of different people. The course is so popular that one does not even need to do a lot of research to choose their preferred colleges, institutes, or academies for their degrees, as they are almost mainstream now.
A graphic design course have objectives:
To train aspirants to become more creative with their visual approach. To train aspirants to be more efficient with the technical aspects of graphics-related tasks and also to acquaint them with relevant aspects of a computer. To train individuals about the various aspects of 2-D and 3-D graphics. To prepare aspirants to become fit for a professional graphic designing profession.
Which course is best for graphic design? Best graphic design courses after 12th - Graphic … Certificate Courses in Graphic Design: Adobe Photoshop. CorelDraw. InDesign. Illustrator. Sketchbook. Figma, etc.
It is possible to become an amateur Graphic Designer who is well on the road to becoming a professional Graphic Designer in about three months. In short, three months is what it will take to receive the professional training required to start building a set of competitive professional job materials.

THE BEST COMPUTER INSTITUTE GOLDEN EDUCATION,ROPNAGAR "PUNJAB"
The best mega DISCOUNT here for your best course in golden education institute in this year.
HURRY UP! GUYS TO JOIN US...
Don't miss the chance
You should go to our institute website
WWW.GOLDEN EDUCATION
CONTACT US: 98151-63600
VISIT IT:
#GOLDEN EDUCATION#INSTITUTE#COURSE#career#best courses#tallyprime#DCA#GRAPHICAL#python#ALL COURSE#ROOPAR
2 notes
·
View notes
Text
Journey to AWS Proficiency: Unveiling Core Services and Certification Paths
Amazon Web Services, often referred to as AWS, stands at the forefront of cloud technology and has revolutionized the way businesses and individuals leverage the power of the cloud. This blog serves as your comprehensive guide to understanding AWS, exploring its core services, and learning how to master this dynamic platform. From the fundamentals of cloud computing to the hands-on experience of AWS services, we'll cover it all. Additionally, we'll discuss the role of education and training, specifically highlighting the value of ACTE Technologies in nurturing your AWS skills, concluding with a mention of their AWS courses.

The Journey to AWS Proficiency:
1. Basics of Cloud Computing:
Getting Started: Before diving into AWS, it's crucial to understand the fundamentals of cloud computing. Begin by exploring the three primary service models: Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS). Gain a clear understanding of what cloud computing is and how it's transforming the IT landscape.
Key Concepts: Delve into the key concepts and advantages of cloud computing, such as scalability, flexibility, cost-effectiveness, and disaster recovery. Simultaneously, explore the potential challenges and drawbacks to get a comprehensive view of cloud technology.
2. AWS Core Services:
Elastic Compute Cloud (EC2): Start your AWS journey with Amazon EC2, which provides resizable compute capacity in the cloud. Learn how to create virtual servers, known as instances, and configure them to your specifications. Gain an understanding of the different instance types and how to deploy applications on EC2.
Simple Storage Service (S3): Explore Amazon S3, a secure and scalable storage service. Discover how to create buckets to store data and objects, configure permissions, and access data using a web interface or APIs.
Relational Database Service (RDS): Understand the importance of databases in cloud applications. Amazon RDS simplifies database management and maintenance. Learn how to set up, manage, and optimize RDS instances for your applications. Dive into database engines like MySQL, PostgreSQL, and more.
3. AWS Certification:
Certification Paths: AWS offers a range of certifications for cloud professionals, from foundational to professional levels. Consider enrolling in certification courses to validate your knowledge and expertise in AWS. AWS Certified Cloud Practitioner, AWS Certified Solutions Architect, and AWS Certified DevOps Engineer are some of the popular certifications to pursue.
Preparation: To prepare for AWS certifications, explore recommended study materials, practice exams, and official AWS training. ACTE Technologies, a reputable training institution, offers AWS certification training programs that can boost your confidence and readiness for the exams.
4. Hands-on Experience:
AWS Free Tier: Register for an AWS account and take advantage of the AWS Free Tier, which offers limited free access to various AWS services for 12 months. Practice creating instances, setting up S3 buckets, and exploring other services within the free tier. This hands-on experience is invaluable in gaining practical skills.
5. Online Courses and Tutorials:
Learning Platforms: Explore online learning platforms like Coursera, edX, Udemy, and LinkedIn Learning. These platforms offer a wide range of AWS courses taught by industry experts. They cover various AWS services, architecture, security, and best practices.
Official AWS Resources: AWS provides extensive online documentation, whitepapers, and tutorials. Their website is a goldmine of information for those looking to learn more about specific AWS services and how to use them effectively.
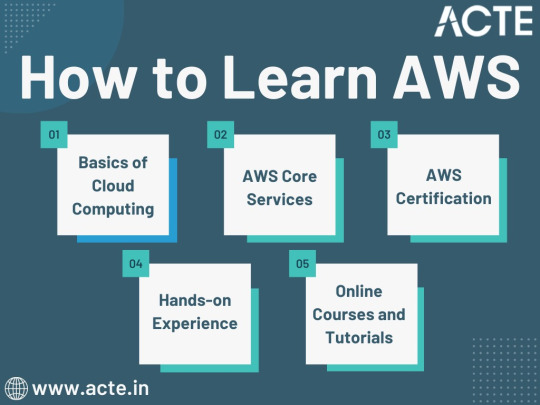
Amazon Web Services (AWS) represents an exciting frontier in the realm of cloud computing. As businesses and individuals increasingly rely on the cloud for innovation and scalability, AWS stands as a pivotal platform. The journey to AWS proficiency involves grasping fundamental cloud concepts, exploring core services, obtaining certifications, and acquiring practical experience. To expedite this process, online courses, tutorials, and structured training from renowned institutions like ACTE Technologies can be invaluable. ACTE Technologies' comprehensive AWS training programs provide hands-on experience, making your quest to master AWS more efficient and positioning you for a successful career in cloud technology.
8 notes
·
View notes
Text
Responsive Design and Beyond: Exploring the Latest Trends in Web Development Services
The two things ruling the present scenario are the internet and smartphones. The easier they are making the lifestyle of the consumers the more difficult it becomes for the lives of the business owners. Digitization has resulted in the rise of competition from the local level to the national and international levels. The businesses that are not adopting the culture are lagging far behind in the growth cycle. The only way to get along with the pace is to hire a custom web development service that is capable of meeting the needs of both the business and consumers. The blog aims to explore some such services that are redefining the web development world.
Latest Trends in the Web Development Services
Blockchain Technology
Blockchain is an encrypted database storing system. It stores information in blocks, which are then joined as a chain. It makes transactions more secure and error-free. The technology enables the participants to make transactions across the internet without the interference of a third party. Thus, this technology can potentially revolutionize different business sectors by reducing the risks of cybercrimes. The technology allows web developers to use open-source systems for their projects, hence simplifying the development process.
Internet of Things (IoT)
IoT can be defined as a network of internet-enabled devices, where data transfer requires no human involvement. It is capable of providing a future where objects are connected to the web. IoT fosters constant data transfer. Moreover, IoT can be used to create advanced communication between different operational models and website layouts. The technology also comes with broad applications like cameras, sensors, and signaling equipment to list a few.
Voice Search Optimization
Voice search optimization is the process of optimizing web pages to appear in voice search. . In the field of web development, the latest innovations are voice-activated self-standing devices, and voice optimization for apps and websites. The technology is being developed that will be able to recognize the voices of different people and provide a personalized AI-based experience
AI-Powered Chatbots
AI-powered chatbot uses Natural Language Processing (NLP) and Machine Learning (ML) to better understand the user’s intent and provide a human-like experience. These have advanced features like 24×7 problem-solving skills and behavior analytics capabilities. These can be effectively used fo customer support to increase customer satisfaction. An AI-powered chatbot can easily be integrated into regular/professional websites and PWAs. Chatbots generally provide quick answers in an emergency and are quick to resolve complaints.
Cloud Computing

It is the use of cloud-based resources such as storage, networking, software, analytics, and intelligence for flexibility and convenience. These services are more reliable as they are backed up and replicated across multiple data centers. This ensures that web applications are always available and running. It is highly efficient for remote working setups. The technology helps avoid data loss and data overload. It also has a low development costs, robust architecture and offers flexibility.
Book a Web Development Service Provider Now
So, if you are also excited to bring your business online and on other tech platforms but are confused about how to do that, you are recommended to reach out to one of the best web development companies i.e. Encanto Technologies. They have a professional and competent web development team that would assist you in the development of an aesthetic, functional, and user-friendly website that would take your revenue to new heights. So, do not wait to enter the online world and book the services of OMR Digital now.
Author’s Bio
This blog is authored by the proactive content writers of Encanto Technologies. It is one of the best professional web development services that embodies a cluster of services including web development, mobile application development, desktop application development, DevOps CI/ CD services, big data development, and cloud development services. So, if you are also looking for any of the web and app development services do not delay any further and contact OMR Digital now.
2 notes
·
View notes
Text
Inventory Management in Manufacturing: How ERP Software Can Help
In the dynamic domain of manufacturing, proficient inventory management plays a crucial role in achieving operational success. Manufacturers endeavour to achieve a nuanced equilibrium between fulfilling customer demand, reducing expenses, and maximising overall operational efficiency. The maintenance of this delicate equilibrium relies on the implementation of efficient and accurate inventory management procedures. In contemporary times, the utilisation of Enterprise Resource Planning (ERP) software has emerged as a paradigm-shifting instrument, fundamentally altering the manner in which manufacturers do inventory management. Stay ahead in the competitive manufacturing landscape. Streamline operations with ERP manufacturing software for small businesses designed and developed by STERP (Shanti Technology).

This blog post explores the complexities of inventory management within the manufacturing industry and emphasises the crucial role that Enterprise Resource Planning (ERP) software plays in enhancing the efficiency of this vital component.
Understanding the Significance of Inventory Management in Manufacturing:
Inventory management encompasses the supervision of a company's inventory, with the objective of optimising the utilisation and replenishment of stockpiled products, while also maximising their overall value. Inventory in the manufacturing industry encompasses three main components: raw materials, work-in-progress (WIP), and finished products. Ensuring an appropriate equilibrium of these constituents is of utmost importance for a multitude of reasons:
· Customer Satisfaction and Demand Fulfillment:
Meeting client demand is crucial for achieving success in the company. The timely availability of appropriate inventory plays a crucial role in ensuring the prompt fulfilment of orders, hence enhancing customer satisfaction and cultivating enduring customer relationships.
· Cost Optimization:
Effective inventory management plays a crucial role in minimising carrying costs, encompassing expenses related to storage, insurance, and obsolescence. This practice guarantees that capital is not needlessly tied up and reduces the likelihood of both excessive inventory and insufficient inventory.
· Production Efficiency:
Production efficiency refers to the ability to maintain an appropriate level of raw materials and components in order to ensure smooth production operations and minimise disruptions caused by material shortages.
· Insightful Decision-making:
The acquisition of precise data regarding inventory levels and patterns offers significant advantages in terms of strategic planning, demand forecasting, and procurement decision-making.
ERP Software for Inventory Management:
Enterprise Resource Planning (ERP) software is designed to consolidate and streamline several corporate operations and functions inside a unified system. Empower your small manufacturing enterprise. Take control of production, inventory, etc. with STERP’s best ERP software for small manufacturing businesses.
In the realm of manufacturing, Enterprise Resource Planning (ERP) assumes a crucial function in augmenting inventory management through the utilisation of the following mechanisms:
· Real-time Inventory Tracking and Visibility:
Real-time inventory tracking and visibility are facilitated by enterprise resource planning (ERP) systems, which offer instantaneous information regarding inventory quantities, locations, and movements. The increased level of visibility enables producers to make well-informed decisions promptly, hence decreasing the probability of experiencing stockouts or having excessive inventory.
· Accurate Demand Forecasting:
Accurate demand forecasting is achieved through the utilisation of advanced analytics and historical data within Enterprise Resource Planning (ERP) systems. This practice guarantees that the manufacturing and procurement processes are in accordance with market demands, hence mitigating the risk of excessive inventory or insufficient supply.
· Automated Reordering and Restocking:
Enterprise Resource Planning (ERP) software facilitates the automation of the reordering process by initiating purchase orders for raw materials or components when inventory levels decline below specified criteria. This automated process enhances operational efficiency and reduces the occurrence of human errors.
· Optimized Order Management:
Efficient order management is facilitated by the integration of order processing and inventory data within an Enterprise Resource Planning (ERP) system. Manufacturers possess the power to allocate priority to orders by considering factors such as the availability of inventory, production capacity, and customer-imposed deadlines. Experience hassle-free manufacturing operations. STERP’s ERP software for the manufacturing industry is designed for manufacturing businesses, providing the tools you need to succeed.
· Enhanced Supplier Collaboration:
Enterprise Resource Planning (ERP) systems provide efficient and effective communication with suppliers, thereby promoting a smooth and uninterrupted flow of goods and services within the supply chain. Manufacturers have the capability to exchange real-time inventory information with suppliers, thereby facilitating enhanced planning and collaboration.
· Effective Risk Management:
The utilisation of Enterprise Resource Planning (ERP) systems facilitates the identification and mitigation of hazards pertaining to the management of inventories. This includes the identification of inventory that is moving at a slow pace, the possibility of becoming obsolete, or irregularities in the quantities of stock.
Maximizing Efficiency with ERP-Enabled Inventory Management:
The utilisation of Enterprise Resource Planning (ERP) software in inventory management enables firms to enhance operational efficiency, decrease expenses, and enhance customer satisfaction. This innovative technology facilitates the adaptation of enterprises to evolving market conditions, enabling them to achieve continuous growth and enhance their competitiveness within the manufacturing industry. The adoption of ERP software for comprehensive inventory management in the evolving manufacturing industry is not merely discretionary, but rather a strategic need. To maintain a competitive advantage, it is imperative to incorporate Enterprise Resource Planning (ERP) systems into manufacturing operations, as this enables the realisation of optimised inventory management capabilities. Enhance productivity without the complexity with STERP’s ERP for manufacturing company – a software specially tailored for manufacturing businesses to simplify the business processes.
#Manufacturing software for small business#Best ERP for small manufacturing business#ERP software for manufacturing industry#ERP for manufacturing company
6 notes
·
View notes
Text
WILL CONTAINER REPLACE HYPERVISOR
As with the increasing technology, the way data centers operate has changed over the years due to virtualization. Over the years, different software has been launched that has made it easy for companies to manage their data operating center. This allows companies to operate their open-source object storage data through different operating systems together, thereby maximizing their resources and making their data managing work easy and useful for their business.

Understanding different technological models to their programming for object storage it requires proper knowledge and understanding of each. The same holds for containers as well as hypervisor which have been in the market for quite a time providing companies with different operating solutions.
Let’s understand how they work
Virtual machines- they work through hypervisor removing hardware system and enabling to run the data operating systems.
Containers- work by extracting operating systems and enable one to run data through applications and they have become more famous recently.

Although container technology has been in use since 2013, it became more engaging after the introduction of Docker. Thereby, it is an open-source object storage platform used for building, deploying and managing containerized applications.
The container’s system always works through the underlying operating system using virtual memory support that provides basic services to all the applications. Whereas hypervisors require their operating system for working properly with the help of hardware support.
Although containers, as well as hypervisors, work differently, have distinct and unique features, both the technologies share some similarities such as improving IT managed service efficiency. The profitability of the applications used and enhancing the lifecycle of software development.
And nowadays, it is becoming a hot topic and there is a lot of discussion going on whether containers will take over and replace hypervisors. This has been becoming of keen interest to many people as some are in favor of containers and some are with hypervisor as both the technologies have some particular properties that can help in solving different solutions.
Let’s discuss in detail and understand their functioning, differences and which one is better in terms of technology?
What are virtual machines?
Virtual machines are software-defined computers that run with the help of cloud hosting software thereby allowing multiple applications to run individually through hardware. They are best suited when one needs to operate different applications without letting them interfere with each other.
As the applications run differently on VMs, all applications will have a different set of hardware, which help companies in reducing the money spent on hardware management.
Virtual machines work with physical computers by using software layers that are light-weighted and are called a hypervisor.
A hypervisor that is used for working virtual machines helps in providing fresh service by separating VMs from one another and then allocating processors, memory and storage among them. This can be used by cloud hosting service providers in increasing their network functioning on nodes that are expensive automatically.
Hypervisors allow host machines to have different operating systems thereby allowing them to operate many virtual machines which leads to the maximum use of their resources such as bandwidth and memory.

What is a container?
Containers are also software-defined computers but they operate through a single host operating system. This means all applications have one operating center that allows it to access from anywhere using any applications such as a laptop, in the cloud etc.
Containers use the operating system (OS) virtualization form, that is they use the host operating system to perform their function. The container includes all the code, dependencies and operating system by itself allowing it to run from anywhere with the help of cloud hosting technology.
They promised methods of implementing infrastructure requirements that were streamlined and can be used as an alternative to virtual machines.
Even though containers are known to improve how cloud platforms was developed and deployed, they are still not as secure as VMs.
The same operating system can run different containers and can share their resources and they further, allow streamlining of implemented infrastructure requirements by the system.
Now as we have understood the working of VMs and containers, let’s see the benefits of both the technologies
Benefits of virtual machines
They allow different operating systems to work in one hardware system that maintains energy costs and rack space to cooling, thereby allowing economical gain in the cloud.
This technology provided by cloud managed services is easier to spin up and down and it is much easier to create backups with this system.
Allowing easy backups and restoring images, it is easy and simple to recover from disaster recovery.
It allows the isolated operating system, hence testing of applications is relatively easy, free and simple.

Benefits of containers:
They are light in weight and hence boost significantly faster as compared to VMs within a few seconds and require hardware and fewer operating systems.
They are portable cloud hosting data centers that can be used to run from anywhere which means the cause of the issue is being reduced.
They enable micro-services that allow easy testing of applications, failures related to the single point are reduced and the velocity related to development is increased.
Let’s see the difference between containers and VMs
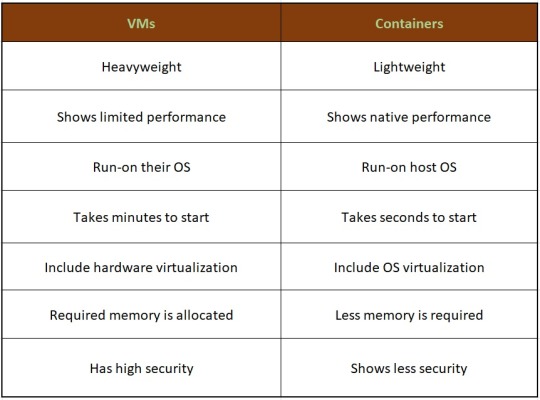
Hence, looking at all these differences one can make out that, containers have added advantage over the old virtualization technology. As containers are faster, more lightweight and easy to manage than VMs and are way beyond these previous technologies in many ways.
In the case of hypervisor, virtualization is performed through physical hardware having a separate operating system that can be run on the same physical carrier. Hence each hardware requires a separate operating system to run an application and its associated libraries.
Whereas containers virtualize operating systems instead of hardware, thereby each container only contains the application, its library and dependencies.
Containers in a similar way to a virtual machine will allow developers to improve the CPU and use physical machines' memory. Containers through their managed service provider further allow microservice architecture, allowing application components to be deployed and scaled more granularly.

As we have seen the benefits and differences between the two technologies, one must know when to use containers and when to use virtual machines, as many people want to use both and some want to use either of them.
Let’s see when to use hypervisor for cases such as:
Many people want to continue with the virtual machines as they are compatible and consistent with their use and shifting to containers is not the case for them.
VMs provide a single computer or cloud hosting server to run multiple applications together which is only required by most people.
As containers run on host operating systems which is not the case with VMs. Hence, for security purposes, containers are not that safe as they can destroy all the applications together. However, in the case of virtual machines as it includes different hardware and belongs to secure cloud software, so only one application will be damaged.
Container’s turn out to be useful in case of,
Containers enable DevOps and microservices as they are portable and fast, taking microseconds to start working.
Nowadays, many web applications are moving towards a microservices architecture that helps in building web applications from managed service providers. The containers help in providing this feature making it easy for updating and redeploying of the part needed of the application.
Containers contain a scalability property that automatically scales containers, reproduces container images and spin them down when they are not needed.
With increasing technology, people want to move to technology that is fast and has speed, containers in this scenario are way faster than a hypervisor. That also enables fast testing and speed recovery of images when a reboot is performed.

Hence, will containers replace hypervisor?
Although both the cloud hosting technologies share some similarities, both are different from each other in one or the other aspect. Hence, it is not easy to conclude. Before making any final thoughts about it, let's see a few points about each.

Still, a question can arise in mind, why containers?
Although, as stated above there are many reasons to still use virtual machines, containers provide flexibility and portability that is increasing its demand in the multi-cloud platform world and the way they allocate their resources.
Still today many companies do not know how to deploy their new applications when installed, hence containerizing applications being flexible allow easy handling of many clouds hosting data center software environments of modern IT technology.
These containers are also useful for automation and DevOps pipelines including continuous integration and continuous development implementation. This means containers having small size and modularity of building it in small parts allows application buildup completely by stacking those parts together.
They not only increase the efficiency of the system and enhance the working of resources but also save money by preferring for operating multiple processes.
They are quicker to boost up as compared to virtual machines that take minutes in boosting and for recovery.
Another important point is that they have a minimalistic structure and do not need a full operating system or any hardware for its functioning and can be installed and removed without disturbing the whole system.
Containers replace the patching process that was used traditionally, thereby allowing many organizations to respond to various issues faster and making it easy for managing applications.
As containers contain an operating system abstract that operates its operating system, the virtualization problem that is being faced in the case of virtual machines is solved as containers have virtual environments that make it easy to operate different operating systems provided by vendor management.
Still, virtual machines are useful to many
Although containers have more advantages as compared to virtual machines, still there are a few disadvantages associated with them such as security issues with containers as they belong to disturbed cloud software.
Hacking a container is easy as they are using single software for operating multiple applications which can allow one to excess whole cloud hosting system if breaching occurs which is not the case with virtual machines as they contain an additional barrier between VM, host server and other virtual machines.
In case the fresh service software gets affected by malware, it spreads to all the applications as it uses a single operating system which is not the case with virtual machines.
People feel more familiar with virtual machines as they are well established in most organizations for a long time and businesses include teams and procedures that manage the working of VMs such as their deployment, backups and monitoring.
Many times, companies prefer working with an organized operating system type of secure cloud software as one machine, especially for applications that are complex to understand.
Conclusion
Concluding this blog, the final thought is that, as we have seen, both the containers and virtual machine cloud hosting technologies are provided with different problem-solving qualities. Containers help in focusing more on building code, creating better software and making applications work on a faster note whereas, with virtual machines, although they are slower, less portable and heavy still people prefer them in provisioning infrastructure for enterprise, running legacy or any monolithic applications.
Stating that, if one wants to operate a full operating system, they should go for hypervisor and if they want to have service from a cloud managed service provider that is lightweight and in a portable manner, one must go for containers.
Hence, it will take time for containers to replace virtual machines as they are still needed by many for running some old-style applications and host multiple operating systems in parallel even though VMs has not had so cloud-native servers. Therefore, it can be said that they are not likely to replace virtual machines as both the technologies complement each other by providing IT managed services instead of replacing each other and both the technologies have a place in the modern data center.
For more insights do visit our website
#container #hypervisor #docker #technology #zybisys #godaddy
6 notes
·
View notes
Text
### LaQuanda Tribe Information Technology (IT) Department Establishment Document
**Document Title**: Establishment of the LaQuanda Tribe Information Technology (IT) Department
**Effective Date**: December 21, 2024
---
**1. Purpose**
The purpose of this document is to outline the establishment of the Information Technology (IT) Department within the LaQuanda Tribe. The IT Department will support the tribe's technological needs, enhance communication, and improve operational efficiency through the effective use of technology.
---
**2. Objectives**
- **Infrastructure Development**: Establish and maintain a robust IT infrastructure to support the tribe's operations and services.
- **Technical Support**: Provide technical support to tribal members and staff for hardware, software, and network issues.
- **Data Management**: Ensure the secure management of tribal data, including storage, backup, and recovery solutions.
- **Cybersecurity**: Implement cybersecurity measures to protect tribal information and technology resources from unauthorized access and threats.
- **Training and Education**: Offer training and resources to enhance the technological skills of tribal members and staff.
---
**3. Organizational Structure**
- **Department Head**: The IT Department will be led by an IT Manager, who will report directly to the tribal council or designated leadership.
- **Staffing**: The department may consist of the following roles:
- IT Support Specialist
- Network Administrator
- Data Analyst
- Cybersecurity Officer
- Systems Administrator
---
**4. Responsibilities**
The IT Department will be responsible for the following functions:
- **Technical Support**: Provide helpdesk support for technical issues faced by members and staff.
- **Network Management**: Oversee the installation, configuration, and maintenance of all network hardware and software.
- **System Administration**: Manage and maintain IT systems, including servers, databases, and applications.
- **Cybersecurity**: Develop and implement security protocols to safeguard the tribe's digital assets.
- **Policy Development**: Create and enforce IT policies and procedures to ensure best practices in technology use and data management.
---
**5. Budget and Funding**
- **Budget Allocation**: The tribal council will allocate an annual budget for the IT Department to cover expenses related to personnel, equipment, software, training, and maintenance.
- **Funding Sources**: Explore additional funding opportunities, including grants, partnerships, and community contributions, to support IT initiatives.
---
**6. Implementation Plan**
- **Needs Assessment**: Conduct an assessment of the tribe's current technology needs and infrastructure.
---
**7. Policy Review**
The establishment document for the IT Department will be reviewed annually to assess its effectiveness and make necessary adjustments based on feedback from tribal members, emerging technologies, and evolving needs.
---
**8. Acknowledgment**
By signing this document, the tribal council affirms its commitment to the establishment of the LaQuanda Tribe Information Technology Department and supports the objectives outlined herein.
---
This document serves as the foundational framework for the establishment of the IT Department within the LaQuanda Tribe, paving the way for enhanced technology management and support for the tribe's initiatives.
0 notes
Text
Understanding Data Encryption and Classification for Effective Data Rights Management
Introduction:
Nowadays, data security has become a top priority. As the data is generated and shared more exponentially, the safeguarding of sensitive information has become more challenging while being crucial. Data encryption and classification are the two major aspects of data rights, and they play a leading part in protecting information from involuntary or Best geofence storage service and in compliance with privacy laws.

What is Data Encryption?
Data encryption is like putting your information in a safe, but it is a digital safe. This process entails encoding the plain text into an illegible text referred to as ciphertext with a specific algorithm and key. This procedure makes sure that even if somebody who's not authorized is granted access to the data, they will still not be able to decrypt it without the corresponding decryption key.
Imagine that you want to send a secret message to your friend. Instead of writing the message clearly, you mix it up using some secret code that only you and your friend know. Without the key, any interposition would only yield nonsensical letters.
What is Data Classification?
Data classification is grouping the data according to its level of sensitivity and significance. It also allows organizations to categorize their data holdings and decide which data needs to be protected at what level. Classification is usually done by tagging data with a label that identifies its security requirements or handling process.
Data classification is like putting your stuff into different boxes. All your important documents might go into a folder, another for pictures and one for miscellaneous notes. Every folder is labelled to indicate what paperwork is inside of it and how you should handle it.
Effective Data Rights Management
Encrypting and classifying data are crucial in the context of the formulation of advice on the management of data rights with the objective of attaining maximum data protection and regulatory compliance. Here's how they work together, Here's how they work together:
Data Identification:
This high classification facilitates to define the sensitive data that needs to be encrypted conveniently. By splitting the data into groups according to the application of encryption technologies, information systems can address the shortage of encryption means and distribute the resources in a reasonable way.
Access Control:
Encryption is a safeguard against unpermitted access, and people with classification rights choose who to give access to encoded information. The access controls can build on data classification labels so that only the laid-out clearance users, possessing the proper clearance can unscramble the cipher and access sensitive information.

Conclusion:
The use of data encryption and classification forms part of comprehensive data rights management plans. Encryption works to make Best Database Backup Services only accessible to authorized people. While at the same time, sensitivity labels can be used to classify easy-to-reach data from data that requires more protection. Organizations can provide an appropriate environment for data if they combine these approaches. They can take care of risks, protect confidential information, and be consistent with data privacy regulations.
#Best object storage software#Best Database backup Services#IT Security services#Cyber security company
0 notes
Text
Why Regular Maintenance of CCTV Systems is Crucial
CCTV systems remain a popular means of security in today’s world, protecting homes, businesses, and public spaces. Slightly, just the installation of the CCTV system does not guarantee lasting safety and efficiency. Maintenance of such a system is important as it may present specific problems that could affect the functionality of the system and compromise its security. Working with the best CCTV company ensures that your system is regularly maintained and operating at its peak performance. Now, let’s discuss its importance and how the regular maintenance of your CCTV system is beneficial for the users – for more information, pay a visit to this link.
1. Ensures Optimal Performance

Like most physical equipment, CCTV systems are known to develop some kinds of wear and tear issues at certain times or periods. This is because their performance may be affected by dust, environmental conditions, or even if the programs were old, they’re operated on old programs. Daily checks need to be made on every part to guarantee that the cameras, the recording devices, and the storage devices are in their best form. Technicians can also check on the images taken such as focus, sharpness and resolution in order to check if the images taken can be used whenever the situation arises.
2. Minimizes System Downtime
Maintenance deferred is one of the greatest risks to face an organization since it exposes the system to the danger of an unplanned downtime. An ineffective camouflaged CCTV is the same as having no CCTV at all because there is always a weak link within the security system which makes your property open to vandals, theft or any criminal. Preventative regular checkups enable the foreman to discover problems yet at an early stage, thus reducing the threat of a significant failure.
3. Enhances Security Coverage
A weak surveillance system, for instance one that has not undergone proper maintenance could have lacks or substandard cameras that do not even record incidences as they happen. Maintenance checks can help confirm that every single camera is well positioned and that no structures or objects obstruct their view, and the areas they capture are the ones intended. Technicians are also able to bend certain angles, change some parts or even reset systems to achieve maximum security results.
4. Prolongs Equipment Lifespan
Purchasing a CCTV system is not cheap, and many times, replacing systems that have been neglected will not be cheap. Service does not only involve putting the system into the optimal state but also in improving its longevity. Cleaning the lenses, tightening the connections that are loose, calibrating the software eliminates the need for repairing or replacement of the lenses and your device in the future.
5. Ensures Compliance with Regulations
In many industries most of which are in the commercial and public sector there is a legal requirement set to ensure there is a functional CCTV system. Maintenance is important as it conforms to the country’s laws and best practices in the sector. It also includes documentation of the different maintenance activities carried out, this may be crucial during the different audits or even during investigations.
6. Cybersecurity Threats Identification and Mitigation

Most of the currently used CCTV systems can use network connections to transmit data, and as is known, such systems can be hacked. During regular maintenance sessions provided by the best CCTV company, updates for both the software and firmware can be implemented, as they are critical in patching common vulnerabilities. The technicians can also review password policies, firewall settings, and encryption options to protect the system against cybercriminals effectively.
7. It also ensures Storage and Backup Systems.
Security footage storage is an important determinant in any CCTV installation, especially for the business entity, which must retain its footage for some time. Maintenance involves confirming storage space and backup functionality as well as reviewing the situation where key footage has been overwritten or simply eliminated. This also proves useful if you need recordings at some point.
8. Reduces Emergency Repair Costs

It leads to reduced expenses on the emergency repairs of structures that have been weakened by heavyEquipment also decreases the likelihood of structural failure and resultant extensive costly repair services.
Emergency types can be rather expensive and inconvenient. Routine maintenance means you are able to identify problems that are small and put them right before they grow into bigger issues. This way, there are no unexpected outages, and the total cost is still cheaper besides enhancing security constantly.
9. Stays Afloat with Modern Technology
The security industry is in a constant state of flux since enhancements in features and solutions enhance the operation of the CCTV systems. Maintenance checks are excellent when it comes to enhancing the part of the system, implementing new functionalities or features or even switching into smarter systems such as AI video surveillance systems. The only way to make certain is to cease adopting any of the modern trends of the system that is already outdated.
10. Creates Confidence with Security Practices
To be sure, your CCTV system is in good condition and working efficiently gives a certain level of reassurance. Whether it regards a house with your family or a store with your investments, a reliable system gives confidence in how you secure your interests. It is usually easier for employees, customers and any other stakeholder to feel secure within a given setting if they see that surveillance systems are actually in operation.
Best Practices for CCTV Maintenance
To ensure your CCTV system remains in top condition, follow these best practices:
Schedule Regular Inspections: Perform annual or even monthly, system checkups by certified technicians who will determine the health of the system.
Clean Components: The camera lens, the connections can also be obstructed by dust and debris therefore regularly clean these parts.
Test the System: Monitor tapes frequently and practice with the alarms, motion sensors, or recording options.
Upgrade Software: Make sure that firmware and software are always the latest and, and the newest so that there is no conflict and the lowest risk of security threats.
Maintain Documentation: Note all maintenance practices with a view of later using the records as references and ensure compliance has been met.
Partner with Experts for Reliable Maintenance
CCTV maintenance can be technically complicated and time-consuming, hence it requires dealing with experienced technicians. The best CCTV installation company in Saudi Arabia and other leading providers supply maintenance plans tailored to your specific requirements. They can discover issues that may not be readily seen during visual inspections and provide quick fixes to ensure the system's properties are preserved. Not only that, but hiring professional maintenance through the best CCTV company ensures you get a well-functioning CCTV system, along with expert advice on improving your security. These professionals offer warranties, provide ongoing support, and assist you in getting the best performance from your system.
Conclusion
Preventive servicing of CCTV systems is not only advisable – it is mandatory. In general, the advantages are obvious – from achieving optimal performance and avoiding any kind of system failure to protecting against cyber risks and increasing the life cycle of the given system. Regardless of whether you are a house owner or a commercial entity owner, embracing maintenance protects your property, properties, and your goodwill.
A well-maintained CCTV system is more than just a security tool; it’s a long-term investment in safety and efficiency. So, don’t wait for a malfunction to remind you of its importance—schedule your next maintenance check today
0 notes
Text
Professional Hadoop Solutions (By: Boris Lublinsky, Kevin T. Smith, Alexey Yakubovich ) With the increasing use of Hadoop all over the world, it becomes necessary for enterprise architects to understand the relationship between Hadoop API and frameworks. They also need to understand that how both of them can be integrated for resolving to real-world issues. With continuous upgradations, this task is not easy. However, a group of Hadoop programmers has come together to offer a practical and detailed guide that enables the user to build and implement these solutions. The members of this team include Boris Lublinsky, a principal architect at Nokia who has written more than 70 publications. The second member is Kevin T. Smith who is working as Director of Technology Solutions at Novetta Solutions where he leads various teams for building data-oriented, highly secure solutions and Alexey Yakubovich, who is a vastly experienced system architect working at Hortonworks. In addition, he is a respected member of Object Management Group SIG on model-driven architecture and SOA governance. Who Should Read This Book? This books is one of the best hadoop books. It is a result of community effort, the main focus of this book is offering a detailed guide that builds and implements various solutions including code-level instructions. The book covers storage of database with HBase and HDFS, data process with MapReduce and automation of data processes with Oozie. This book also covers in-depth information regarding Hadoop security, automation of Hadoop processes in real-time and running on Hadoop with Amazon Web Services. The book is rich with examples in XML and Java. Further, it covers the usage of APIs and their inner workings. As this book offers comprehensive information about the Hadoop ecosystem, it is easy to assume that this book is primarily targeted towards developers, architects, and designers, who are the main players in building and developing Hadoop software system and require information to utilize the fabulous power of this software. What Is Good About This Book? With increasing use of Hadoop, it has become necessary for people who work primarily with massively scalable analytics to understand the power of Hadoop technologies and take its advantage for building and implementing real-time solutions. As this book is primarily targeted towards developers, architects and designers who are involved in building Hadoop software systems, this book is the primary operations guide that can be used as a reference to tackling any situation. The users will learn how to build advanced enterprise applications and code-level information for delivering real-world solutions. It provides information regarding data designing and its impact upon implementation. Further, readers will know about the functioning of MapReduce and reformulate various business issues in MapReduce. To make it easy for the users, the authors have included Java code examples that can be used in real-life situations. These Java codes have been derived from various applications that have been built by these authors and deployed in organizations. Additionally, it covers various approaches that can be used for successful running of Hadoop in AWS or Amazon Web Services. The book showcases how to extend the capabilities of Hadoop’s security including auditing, SSO or Single-Sign-On, authorization, authentication, and encryption. Further, it offers information on building Hadoop-based applications in real-time. To ensure this, a team of highly experienced Hadoop specialists has collaborated on this book. Although this book is directed towards the experienced programmers, the beginner can also use this book as a reference. It is because the authors have used very easy language and extensive code examples in XML and Java for users. All in all, this is a must have a book in the reference library of a Hadoop developers, designers, and architects. What Is Not So Good About This Book?
This book has certain downsides. For instance, although this book offers exhaustive information about a vast range of Hadoop relates topics, it has some editing issues. This is because some of the code samples are broken; the typos are another issue throughout the book. Some of them can also be found in the source code. Some of the source codes that are given in the book do not work in real-life. However, these are minor issues and can be easily tackled by experienced architects. A reference book that allows readers to tap the vast power of Hadoop in order to utilize it for various projects, it’s a must-have for architects, designers, and developers. Broadly, other than them, the book is targeted towards anyone who would like to understand the intricacies of the software.
0 notes
Text
Streamline Your Onboarding Process with the Ultimate Client Playbook
Client onboarding is a crucial phase in establishing long-term partnerships. It’s the first step where trust, expectations, and deliverables are set in motion. A seamless onboarding process not only impresses your clients but also ensures operational efficiency, reduced errors, and enhanced client satisfaction. By integrating Professional Services Automation (PSA) software, you can streamline onboarding like never before, creating a consistent and scalable approach.
Here’s how to build an ultimate client onboarding playbook with the power of PSA software.
Why a Client Onboarding Playbook Matters
An onboarding playbook is a structured framework that guides your team and clients through the onboarding journey. It helps ensure:
Consistency: Every client receives the same high-quality onboarding experience.
Transparency: Expectations, timelines, and deliverables are clearly defined.
Efficiency: Processes are streamlined, reducing time and manual errors.
For professional services, where workflows can be complex and client needs unique, leveraging a playbook supported by PSA software transforms onboarding into a smooth, repeatable process.
Building the Ultimate Client Onboarding Playbook
1. Pre-Onboarding Preparation
Gather Client Information: PSA software allows you to centralize client data, such as contracts, goals, and contact details, in one accessible location.
Standardize Processes: Use templates within the PSA system to create repeatable workflows for different types of clients.
2. Kick-Off Meetings
Schedule kick-off meetings through PSA scheduling tools and send automated reminders.
Share agendas and assign tasks to team members, ensuring alignment on objectives and deliverables.
3. Document Management
PSA software simplifies document sharing and storage. Use it to request, store, and manage contracts, compliance forms, and other onboarding materials in a secure, organized manner.
4. Role Assignments and Resource Allocation
Assign roles to team members directly in the PSA system, ensuring clarity and accountability.
Allocate resources based on availability and project requirements, ensuring optimal utilization from day one.
5. Milestone Setting and Progress Tracking
Break the onboarding process into smaller, measurable milestones.
Use PSA dashboards to monitor the progress of each milestone and automate reminders for pending tasks.
The Role of PSA Software in Onboarding
PSA software is a game-changer in client onboarding, offering features that enhance the process at every step:
Automation: Automate repetitive tasks, such as sending welcome emails, onboarding reminders, and follow-ups.
Centralized Data: Keep all client-related information in one place, improving accessibility and reducing duplication.
Real-Time Visibility: Provide clients and internal teams with real-time updates on onboarding progress.
Collaboration: Enable cross-functional teams to collaborate seamlessly within the PSA platform.
Best Practices for Streamlined Onboarding
Personalize the Experience
Tailor onboarding workflows to suit individual client needs. PSA software enables customization without deviating from standardized processes.
Set Realistic Expectations
Use PSA tools to provide clients with clear timelines, deliverables, and what they can expect during the onboarding phase.
Train Your Clients
Schedule training sessions through PSA software, ensuring clients understand your processes, tools, or systems.
Collect Feedback
Once onboarding is complete, use PSA analytics to gather client feedback and identify areas for improvement.
Benefits of Using PSA Software for Client Onboarding
Efficiency Gains: Automation reduces manual effort, saving time and resources.
Consistency: Every client receives a uniform, high-quality experience.
Data-Driven Decisions: Analytics from PSA software help refine and improve onboarding workflows.
Improved Client Satisfaction: A seamless process leaves a lasting positive impression.
Conclusion
Streamlining client onboarding is essential for professional services firms aiming to deliver exceptional experiences. By incorporating PSA software into your onboarding playbook, you can automate workflows, centralize information, and improve client satisfaction. A well-executed onboarding process is not only a strong start to the client relationship but also a competitive advantage.
Transform your onboarding today with the power of PSA software and ensure every client journey begins with confidence, clarity, and success.
0 notes
Text
Comprehensive Overview of Techniques and Tools in Data Analysis
Data analysis plays a pivotal role in uncovering insights, driving decisions, and fostering business growth. With the increasing importance of data-driven strategies, understanding the techniques and tools used in data analysis has become essential. This comprehensive guide explores key data analysis techniques and popular tools used by professionals across industries.
Data Analysis Techniques
1. Descriptive Analysis
Descriptive analysis summarizes data by providing insights into past events. Techniques include:
Data Summarization: Using measures like mean, median, and mode.
Data Visualization: Charts, graphs, and dashboards.
Trend Analysis: Identifying historical patterns.
2. Exploratory Data Analysis (EDA)
EDA involves examining datasets to uncover underlying patterns, relationships, and anomalies. Techniques include:
Data Cleaning: Removing inaccuracies and filling missing values.
Data Profiling: Summarizing data characteristics.
Outlier Detection: Identifying and handling unusual data points.
3. Inferential Analysis
This technique uses statistical models to infer properties about a population based on sample data. Key methods include:
Hypothesis Testing: Assessing assumptions about data.
Regression Analysis: Understanding relationships between variables.
Confidence Intervals: Estimating population parameters.
4. Predictive Analysis
Predictive analysis forecasts future outcomes using historical data. Techniques include:
Machine Learning Models: Regression, classification, and clustering.
Time Series Analysis: Forecasting future trends.
Predictive Modeling: Developing statistical models.
5. Prescriptive Analysis
Prescriptive analysis recommends actions based on data-driven insights. Methods include:
Optimization Models: Suggesting the best course of action.
Simulation Models: Evaluating different scenarios.
Decision Trees: Visualizing decision-making processes.
Popular Tools for Data Analysis
1. Spreadsheets (Excel, Google Sheets)
Widely used for basic data analysis tasks such as summarization, filtering, and visualization.
2. Statistical Software (R, SAS, SPSS)
R: An open-source language for statistical computing and graphics.
SAS: Advanced analytics and business intelligence software.
SPSS: Popular for social science data analysis.
3. Data Visualization Tools (Tableau, Power BI)
Tableau: Interactive dashboards and real-time visual analytics.
Power BI: Data visualization and business intelligence reporting.
4. Database Management Tools (SQL, MySQL, PostgreSQL)
SQL-based tools enable querying and managing structured datasets.
5. Big Data Tools (Apache Hadoop, Apache Spark)
Hadoop: Distributed storage and processing of large datasets.
Spark: Fast data processing for large-scale analytics.
6. Programming Languages (Python, R)
Python: Popular for machine learning, data manipulation, and visualization.
R: Preferred for statistical analysis and data modeling.
7. Business Intelligence Platforms (Looker, Qlik)
Looker: Data exploration and business intelligence platform.
Qlik: Self-service data visualization and guided analytics.
8. Cloud Platforms (Google Cloud, AWS, Azure)
Provide scalable storage, data processing, and machine learning services.
Best Practices for Data Analysis
Define Objectives: Clearly outline the goals and questions to address.
Data Collection: Ensure accurate, reliable, and relevant data sources.
Data Cleaning: Remove inconsistencies and prepare data for analysis.
Data Visualization: Use intuitive visuals to communicate findings.
Model Selection: Choose appropriate models and techniques.
Insight Communication: Present findings with actionable recommendations.
Conclusion
Data analysis is a critical skill in today’s digital world, driving decisions across business, research, and technology sectors. By mastering essential techniques and leveraging powerful tools, organizations can unlock the true potential of their data, enabling informed decision-making and sustained growth.
0 notes
Text
Best IT Service Provider in Faridabad
Businesses in the fast-paced digital world have to keep up with the changing tides and be one step ahead to remain competitive in a challenging market. Faridabad, a rising business and technology hub in the Delhi NCR region, houses numerous companies seeking reliable IT services. Modulation Digital is the best IT service provider in Faridabad that offers an all-inclusive array of services to cater to the different needs of startups, SMBs, and large enterprises.
Why Choose Modulation Digital as Your IT Partner?
The role of a good IT service provider is far beyond just troubleshooting. At Modulation Digital, the focus is on creating value through cutting-edge solutions that enhance business growth, streamline operations, and ensure smooth digital transformation. Here's why Modulation Digital is your ideal IT partner in Faridabad:
1. Holistic IT Solutions
Modulation Digital offers a range of IT services and is, therefore, a one-stop shop for businesses looking to modernize their operations. The service portfolio includes:
Web Design and Development: Stunning, user-friendly websites that perfectly fit your brand identity.
Digital Marketing: Improving your online presence through SEO, social media marketing, PPC campaigns, and more.
Custom Software Development**: Building customized software solutions to meet the unique needs of your business.
Cloud Services: Provide safe cloud storage, migration, and management to optimize data accessibility and security.
IT Infrastructure Management: Optimal IT operations based on the principles of effective monitoring and maintenance.
2. Solutions for Every Business
At Modulation Digital, a belief is always held that no business is ever the same; hence, requires a customized solution. The company takes some time to get to understand your business objectives, sector challenges, and customer population to come up with measurable solutions. No matter your size, either as a local startup or an established corporation, Modulation Digital keeps your IT systems running harmoniously to accelerate growth.
3. Experienced Team of Experts
What makes Modulation Digital stand out is its team of highly skilled professionals. With extensive experience in web design, software development, digital marketing, and IT management, the team is well prepared to handle complex projects and deliver excellence time and again. This dedication to expertise has earned Modulation Digital the reputation of being the best IT service provider in Faridabad.
4. Customer-Centric Approach
Customer satisfaction is at the forefront of everything that Modulation Digital does. The agency creates lasting, meaningful relationships with its clients through customized services and maintaining the transparency of the process. It maintains regular communication, keeps clients updated about things in due time, and ensures support for all of them.
5. Innovation Commitment
Staying ahead in the tech world requires constant innovation, and Modulation Digital embraces this wholeheartedly. By leveraging the latest technologies, tools, and frameworks, the team delivers future-ready solutions that keep your business competitive and resilient.
Services That Define Excellence
1. Web Design and Development
A business's website is often the first impression it makes on a potential customer. Modulation Digital excels in creating visually appealing, responsive, and performance-driven websites that not only attract visitors but also convert them into loyal customers. The focus is on blending creativity with functionality to build a digital platform that aligns with your brand's vision.
Key offerings include:
E-commerce website development
Content management systems (CMS)
Website redesign and optimization Custom web application development
2. Digital Marketing
In a world where most of the interactions are online, digital marketing is the need of the hour for any business to stay in the game. As the Best IT Service Provider in Faridabad, Modulation Digital offers a full suite of digital marketing services that are designed to boost your online presence, engage your audience, and drive conversions.
The digital marketing services include:
Search Engine Optimization (SEO): Improves your website's ranking in search results to attract organic traffic.
Social Media Marketing (SMM): Develop your social media presence to engage with customers.
PPC campaigns: producing targeted leads using cost-efficient advertising.
Email Marketing: Develop a relationship with your customers with personalized email campaigns.
Content marketing: high-quality content that is well-related to target audiences.
Businesses today rely heavily on technology, making IT infrastructure a vital component of operations. Modulation Digital provides end-to-end IT infrastructure management services to make sure your systems are up and running at all times.
Services include;
Network setup and monitoring
Data backup and recovery solutions
Cybersecurity measures that will protect against threats
IT consulting that deals with strategy and implementation.
3. Cloud Services
The business and its data storage have now taken an upsurge in terms of cloud computing. Modulation Digital helps companies shift to the cloud with ease and scalable and secure cloud solutions for them. It may offer cloud storage, SaaS integration, or hybrid cloud solutions. Whatever your data needs, it makes it safe and easily accessible to you.
4. Custom Software Development
No two businesses are alike, and off-the-shelf software often falls short of meeting specific requirements. Modulation Digital specializes in custom software development, creating solutions that are tailored to your unique needs. From enterprise resource planning (ERP) systems to customer relationship management (CRM) software, the agency builds tools that enhance efficiency and productivity.
Industries Served
As the Best IT Service Provider in Faridabad, Modulation Digital serves various industries, including:
Retail and E-commerce: Developing robust e-commerce platforms and enhancing online shopping experiences.
Healthcare: Providing IT solutions for patient management, telemedicine, and data security.
Education: Creating e-learning platforms and digital tools for educational institutions.
Real Estate: Building websites and apps that simplify property listings and transactions.
Hospitality: Tailoring IT solutions to increase customer involvement.
Business Transformation in Faridabad
Modulation Digital has been highly influential in changing businesses all over Faridabad in terms of the adoption of digital solutions. Here are some real-world examples through which the agency has managed to make a difference in the market:
1. Increasing Sales Online for E-commerce Companies
Modulation Digital has assisted several e-commerce businesses to boost their sales and customer retention by implementing advanced SEO strategies and optimizing their websites for conversions.
2. Optimization of Operations for Enterprises
Modulation Digital has empowered large enterprises with custom software solutions that help automate their processes, improve collaboration, and reduce operational costs.
3. Empowering Startups with Digital Strategies
For startups in Faridabad, Modulation Digital is the perfect launchpad by offering affordable IT solutions, from web development to marketing campaigns.
The Modulation Digital Advantage
When you partner with Modulation Digital, you are not just investing in IT services; you are investing in a brighter future for your business. Here's what you gain:
Expert Guidance: Access to a team of professionals who are experts in their fields.
Scalability: Solutions that grow with your business.
Cost-effectiveness: Affordable services deliver maximum ROI.
Reliability: Dependable support ensures the system is always functional.
CONCLUSION
Being one of the best IT service providers in Faridabad, Modulation Digital provides businesses with the power to help them achieve their goals by harnessing the power of technology. Client-first approach, innovative solutions, and a proven track record set Modulation Digital as your trusted partner for elevating your business to new heights.
Whether you need beautifully designed websites, robust IT infrastructures, or comprehensive digital marketing strategies, Modulation Digital has it all for you. Experience the difference with Modulation Digital and let your business thrive in the digital age.
Contact Modulation Digital today and take that first step toward transforming your business!
#ITservices#Faridabad#technology#ITsupport#ITsolutions#digitaltransformation#businesssolutions#managedservices#cloudcomputing#cybersecurity#networking#innovation#ITconsulting#ITexpert#ITpartner#ITcompany#ITindustry#ITprofessionals#ITconsultants#IToutsourcing
0 notes
Text
What is object storage software? Uses and benefits of object storage software

Best Object Storage Software
Object storage software is transforming the way organisations manage and store their data. Also, it has become the new demand of the market, and every business needs to invest in it. It is something unlike traditional file systems or blocks storage; object storage treats data as objects, making it a versatile solution for various industries and applications. In this guest post, we will explore the uses and benefits of object storage software and highlight how it can transform data management in the digital age.
Let's read it out:
What is object storage software?
Before starting anything, you must know exactly what Best Object Storage Software is. It is a data storage architecture designed to manage, store, and retrieve unstructured data as objects rather than traditional file hierarchies or block storage. In the last few years, it has gained importance just because of its flexibility, scalability, and suitability for handling vast amounts of data.
Uses of Object Storage Software:
Cloud Storage and Backup:
Object storage works as the backbone of many cloud storage services. It offers businesses secure storage and retrieval of data in a scalable and cost-effective manner, making it ideal for backup solutions and data archiving.
Media and Entertainment:
In the field of media and entertainment businesses, they use object storage to manage libraries of content like images, videos, audio, and many other files. Its ability to handle large files and metadata efficiently makes it an essential tool for content creators and broadcasters.
Healthcare and Life Sciences:
In the health sector, object storage is used for managing medical images, research data, and patient records. Because this sector must protect the data and scalability of the function, where data integrity and accessibility are important.
IoT Data Management:
With the explosion of IoT devices, object storage has gained new importance in collecting, storing, and analysing the massive volume of data generated by these devices. It offers a reliable and scalable solution for IoT data management.
Content Delivery:
Content delivery networks (CDNs) use object storage to effectively distribute material to end users throughout the globe. Access to multimedia content is guaranteed to have low latency due to its global distribution.
Benefits of Object Storage Software:
Accordingly, there are lots of benefits to using object storage software. Below, we have mentioned some of them:
Scalability:
Object storage is highly scalable; it allows organisations to seamlessly expand their storage capacity as data volumes grow. And you can understand that this scalability is very crucial in this data-driven world.
Cost-Effective Storage:
Because object storage enables businesses to pay for the storage they use, it provides affordable alternatives. Its capacity to hold large files effectively also lessens the need for expensive data management.
Data Redundancy and Durability:
Object storage's integrated replication and erasure coding enable data redundancy and durability. This guarantees data availability and integrity even in the event of hardware malfunctions.
Handling Metadata:
Every item in object storage has associated metadata that offers useful details about the data. For effective data indexing, searching, and retrieval, this metadata is essential.
Easy Integration:
Object storage systems are simple to include in current processes and applications since they are compatible with a wide range of APIs and protocols.
Data Accessibility:
Remote work and collaboration are made easier by object storage, which provides easy access to data from any location. For effective data retrieval, versioning and data tiering are also supported.
Conclusion
Object storage software has developed into a vital resource for businesses handling enormous data volumes. It is an invaluable tool in many businesses due to its adaptability, scalability, affordability, and data management skills. Businesses looking for dependable and effective data management solutions must comprehend object storage software and learn how to use it as data volumes continue to rise. If you are looking for the Best Object Storage Software service provider, you can connect with us here and get the best services.
0 notes